Visualogyx for Financial Services
AI-Powered
Risk Mitigation &
Asset Validation
Collateral & Asset Verification Software with Advanced "Know Your Product" (KYPIT) Authentication.
Get Your Free KYPiT-Enabled Demo
Revolutionize your collateral asset validation processes with our cutting-edge "Know Your Product" technology.
Visualogyx for Financial Services
AI-Powered
Risk Mitigation &
Asset Validation
Collateral & Asset Verification Software with Advanced "Know Your Product" (KYPIT) Authentication.
Get Your Free KYPiT-Enabled Demo
Revolutionize your collateral asset validation processes with our cutting-edge "Know Your Product" technology.

Reduce Operational Risk with KYPiT Authentication
Our KYPiT authentication layer identifies potential fraud risks and discrepancies during inspections.

Increase Visibility in Your Virtual Field Exams
Achieve a unified, trustworthy data source for your collateral and field exams backed by KYPiT's authentication technology.

Transform Your Financial Services with Digital Inspections
Eliminate paper trails and manual validations, significantly lowering operational costs .
Collateral & Asset Verification Software
Visualogyx is transforming how financial institutions conduct Collateral and Asset Validations. Similar to how firms rely on "Know Your Customer" (KYC) protocols, our KYPIT authentication layer allows you to "Know Your Product" by collecting and authenticating data evidence during field exams.
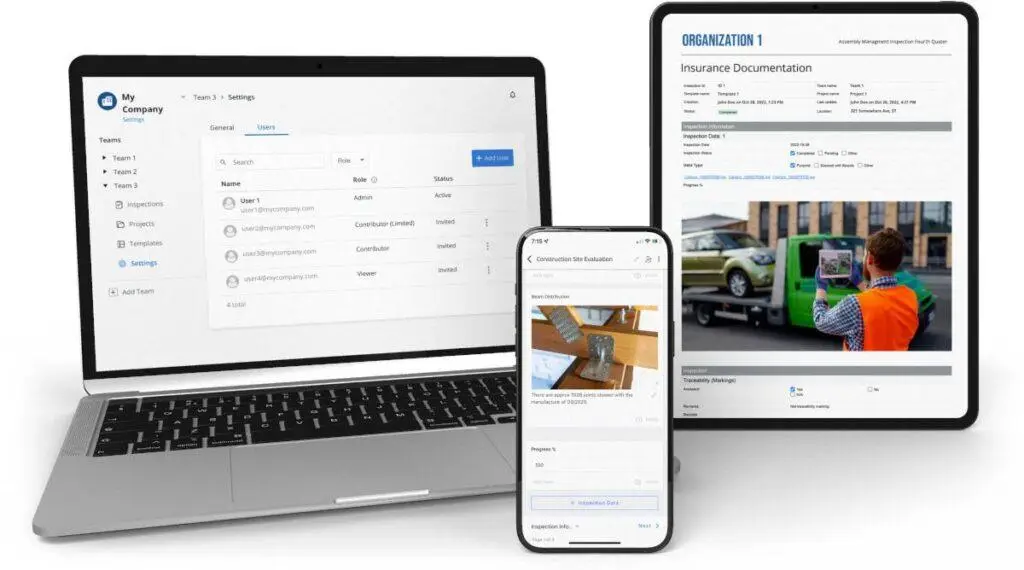
- Customized Validation Forms for Collateral Assessment
- Real-Time Multimedia Data Capture
- Instant Compliance Reports
- Mobile and Web-Based Solutions
- Collaborative Teams on Verification Projects
- Track Record of Inspection Activities
- Metadata Inspection Analysis with KYPiT
How It Works


Dispatch
Utilizing Visualogyx's inspection-sharing functionality, your team can assign predefined forms to field inspectors, final clients, or third-party auditors.


Inspect
The assigned party is notified when an inspection is ready for them. They follow instructions and upload the requested asset data using the Visualogyx mobile app.

Verify
After inspections, our KYPiT authentication layer detects metadata discrepancies, enhancing asset authentication and fraud prevention.
Inspections with Metadata Cognition and Analysis

Unlocking Trust in Your Assets and Collateral Validations
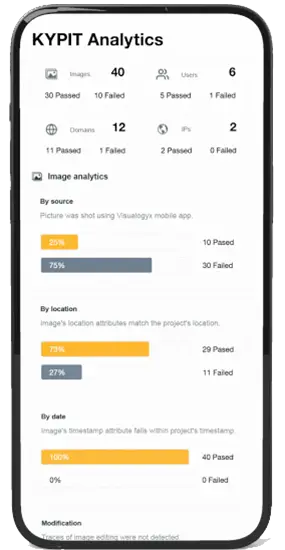
KYPiT, an AI layer positioned above a Visualogyx report aids in verifying inspection metadata and detecting potential discrepancies or fraudulent activities.
Image Metadata Authentication
Image metadata such as location, source, and timestamps are cross-checked with inspections.
Geolocation
Assigned inspections can be allocated to specific locations and cross-referenced with inspection metadata.
Examiner or inspector Verification
Information about users who engage with the field exam, such as their email and mobile number, is authenticated.
Web integrity Check
Web information, such as domains and IPs interacting with the inspection, undergoes validation.
Visualogyx for Financial Services
Optimize field exams and inspection processes with Visualogyx, enabling the authentication of vulnerable assets.
Functions
- Credit Underwriting
- Loan Origination
- Risk Management
- Insurance Claims Processing
- Asset Valuation
- Fraud Prevention
- Asset Recovery
- Inventory Verification
- Vehicle Assessments
Industries
- Banking
- Insurance
- Buy Now Pay Later
- Hard Money Lending
- HELOC Lending
- Auto Financing & Leasing
- Real Estate
- Inventory Financing
- Pawn Shops


